-->
Configure Adobe Identity Management to support provisioning with Azure AD. Login to Adobe Admin Console. Navigate to Settings Directory Details Sync. Select Sync users from Microsoft Azure and click Next. Copy and save the Tenant URL and the Secret token. Visit our downloads page on a Windows machine. In the Outlook tile, click Download to download the Virtru installation file. (If you are not on a Windows machine, you will be prompted to visit the page on a Windows device). Click Run to give permission to run the installer VirtruForOutlookInstaller.msi.
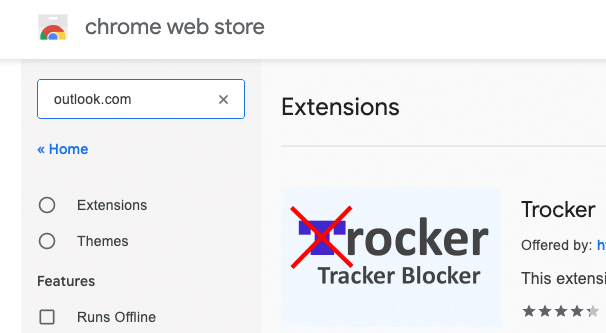
Adobe Sign Extension For Outlook
This tutorial describes the steps you need to perform in both Adobe Identity Management and Azure Active Directory (Azure AD) to configure automatic user provisioning. When configured, Azure AD automatically provisions and de-provisions users and groups to Adobe Identity Management using the Azure AD Provisioning service. For important details on what this service does, how it works, and frequently asked questions, see Automate user provisioning and deprovisioning to SaaS applications with Azure Active Directory.
Adobe Extension For Outlook
Capabilities supported
- HOW TO USE EXTENSION MANAGER CS6. Download the Extension Manager CS6. Download the Extension Manager CC installer and save it to your machine. Double-click the installer to begin the installation process. Return to Adobe.com to Download Extensions. Follow the instructions to install and run the Adobe Exchange Panel.
- Adobe Creative Cloud and Microsoft Teams bring creative work and teamwork together. With the Creative Cloud app for Microsoft Teams, designers can easily share their work, get feedback and stay up-to-date on actions taken on their assets all within Microsoft Teams.
- Adobe Sign is Microsoft’s preferred e-signature solution that gets your documents signed faster than ever when you add it to your Microsoft Outlook ribbon. Now, you can send a document for e-signature and track the signing process at every step directly from within Outlook.

- Create users in Adobe Identity Management
- Remove users in Adobe Identity Management when they do not require access anymore
- Keep user attributes synchronized between Azure AD and Adobe Identity Management
- Provision groups and group memberships in Adobe Identity Management
- Single sign-on to Adobe Identity Management (recommended)

Prerequisites
The scenario outlined in this tutorial assumes that you already have the following prerequisites:
- An Azure AD tenant.
- A user account in Azure AD with permission to configure provisioning (for example, Application Administrator, Cloud Application administrator, Application Owner, or Global Administrator).
- A federated directory in the Adobe Admin Console with verified domains.
- Review the adobe documentation on user provisioning
Adobe Acrobat Extension For Outlook
Note

If your organization uses the User Sync Tool or a UMAPI integration, you must first pause the integration. Then, add Azure AD automatic provisioning to automate user management from the Azure Portal. Once Azure AD automatic provisioning is configured and running, you can completely remove the User Sync Tool or UMAPI integration.
Step 1. Plan your provisioning deployment
- Learn about how the provisioning service works.
- Determine who will be in scope for provisioning.
- Determine what data to map between Azure AD and Adobe Identity Management.
Step 2. Configure Adobe Identity Management to support provisioning with Azure AD
Login to Adobe Admin Console. Navigate to Settings > Directory Details > Sync.
Click Add Sync.
Select Sync users from Microsoft Azure and click Next.
Copy and save the Tenant URL and the Secret token. These values will be entered in the Tenant URL and Secret Token fields in the Provisioning tab of your Adobe Identity Management application in the Azure portal.
Step 3. Add Adobe Identity Management from the Azure AD application gallery
Add Adobe Identity Management from the Azure AD application gallery to start managing provisioning to Adobe Identity Management. If you have previously setup Adobe Identity Management for SSO, you can use the same application. However it is recommended that you create a separate app when testing out the integration initially. Learn more about adding an application from the gallery here.
Step 4. Define who will be in scope for provisioning
The Azure AD provisioning service allows you to scope who will be provisioned based on assignment to the application and or based on attributes of the user / group. If you choose to scope who will be provisioned to your app based on assignment, you can use the following steps to assign users and groups to the application. If you choose to scope who will be provisioned based solely on attributes of the user or group, you can use a scoping filter as described here.
When assigning users and groups to Adobe Identity Management, you must select a role other than Default Access. Users with the Default Access role are excluded from provisioning and will be marked as not effectively entitled in the provisioning logs. If the only role available on the application is the default access role, you can update the application manifest to add additional roles.
Start small. Test with a small set of users and groups before rolling out to everyone. When scope for provisioning is set to assigned users and groups, you can control this by assigning one or two users or groups to the app. When scope is set to all users and groups, you can specify an attribute based scoping filter.
Step 5. Configure automatic user provisioning to Adobe Identity Management
This section guides you through the steps to configure the Azure AD provisioning service to create, update, and disable users and/or groups in TestApp based on user and/or group assignments in Azure AD.
To configure automatic user provisioning for Adobe Identity Management in Azure AD:
Sign in to the Azure portal. Select Enterprise Applications, then select All applications.
In the applications list, select Adobe Identity Management.
Select the Provisioning tab.
Set the Provisioning Mode to Automatic.
Under the Admin Credentials section, input your Adobe Identity Management Tenant URL and Secret Token retrieved earlier from Step 2. Click Test Connection to ensure Azure AD can connect to Adobe Identity Management. If the connection fails, ensure your Adobe Identity Management account has Admin permissions and try again.
In the Notification Email field, enter the email address of a person or group who should receive the provisioning error notifications and select the Send an email notification when a failure occurs check box.
Select Save.
Under the Mappings section, select Synchronize Azure Active Directory Users to Adobe Identity Management.
Review the user attributes that are synchronized from Azure AD to Adobe Identity Management in the Attribute-Mapping section. The attributes selected as Matching properties are used to match the user accounts in Adobe Identity Management for update operations. If you choose to change the matching target attribute, you will need to ensure that the Adobe Identity Management API supports filtering users based on that attribute. Select the Save button to commit any changes.
Attribute Type userName String emails[type eq 'work'].value String active Boolean addresses[type eq 'work'].country String name.givenName String name.familyName String urn:ietf:params:scim:schemas:extension:Adobe:2.0:User:emailAliases String Under the Mappings section, select Synchronize Azure Active Directory Groups to Adobe Identity Management.
Review the group attributes that are synchronized from Azure AD to Adobe Identity Management in the Attribute-Mapping section. The attributes selected as Matching properties are used to match the groups in Adobe Identity Management for update operations. Select the Save button to commit any changes.
Attribute Type displayName String members Reference To configure scoping filters, refer to the following instructions provided in the Scoping filter tutorial.
To enable the Azure AD provisioning service for Adobe Identity Management, change the Provisioning Status to On in the Settings section.
Define the users and/or groups that you would like to provision to Adobe Identity Management by choosing the desired values in Scope in the Settings section.
When you are ready to provision, click Save.
This operation starts the initial synchronization cycle of all users and groups defined in Scope in the Settings section. The initial cycle takes longer to perform than subsequent cycles, which occur approximately every 40 minutes as long as the Azure AD provisioning service is running.
Step 6. Monitor your deployment
Once you've configured provisioning, use the following resources to monitor your deployment:
- Use the provisioning logs to determine which users have been provisioned successfully or unsuccessfully
- Check the progress bar to see the status of the provisioning cycle and how close it is to completion
- If the provisioning configuration seems to be in an unhealthy state, the application will go into quarantine. Learn more about quarantine states here.
Additional resources
Next steps
In the Adobe Send & Track group, click Attach File via Adobe Send & Track.
Note:The plug-in does not work if you have RTF set as the default formatting for email messages. To use the plug-in, switch to HTML formatting.
Browse and select the files that you want to attach, and then click Open.
Alternatively, you can drag files from folders on your computer and drop them on the message window. A prompt appears in the right side of the attachment input box asking whether you want to attach files via Adobe Send & Track. Click Yes.
If you’re not signed in, you see a prompt. Click OK. Open Acrobat, click the Sign In link at the upper-right corner and then sign in with your Adobe ID and password.
The selected files are uploaded to Adobe Send & Track, and public links to the files are inserted in the message body.
You can modify the text shown in black to be anything you want, and move the text into another part of your email. Be careful not to modify the link.